Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are Information Security Team OKRs?
The OKR acronym stands for Objectives and Key Results. It's a goal-setting framework that was introduced at Intel by Andy Grove in the 70s, and it became popular after John Doerr introduced it to Google in the 90s. OKRs helps teams has a shared language to set ambitious goals and track progress towards them.
Formulating strong OKRs can be a complex endeavor, particularly for first-timers. Prioritizing outcomes over projects is crucial when developing your plans.
We've tailored a list of OKRs examples for Information Security Team to help you. You can look at any of the templates below to get some inspiration for your own goals.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect Information Security Team OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
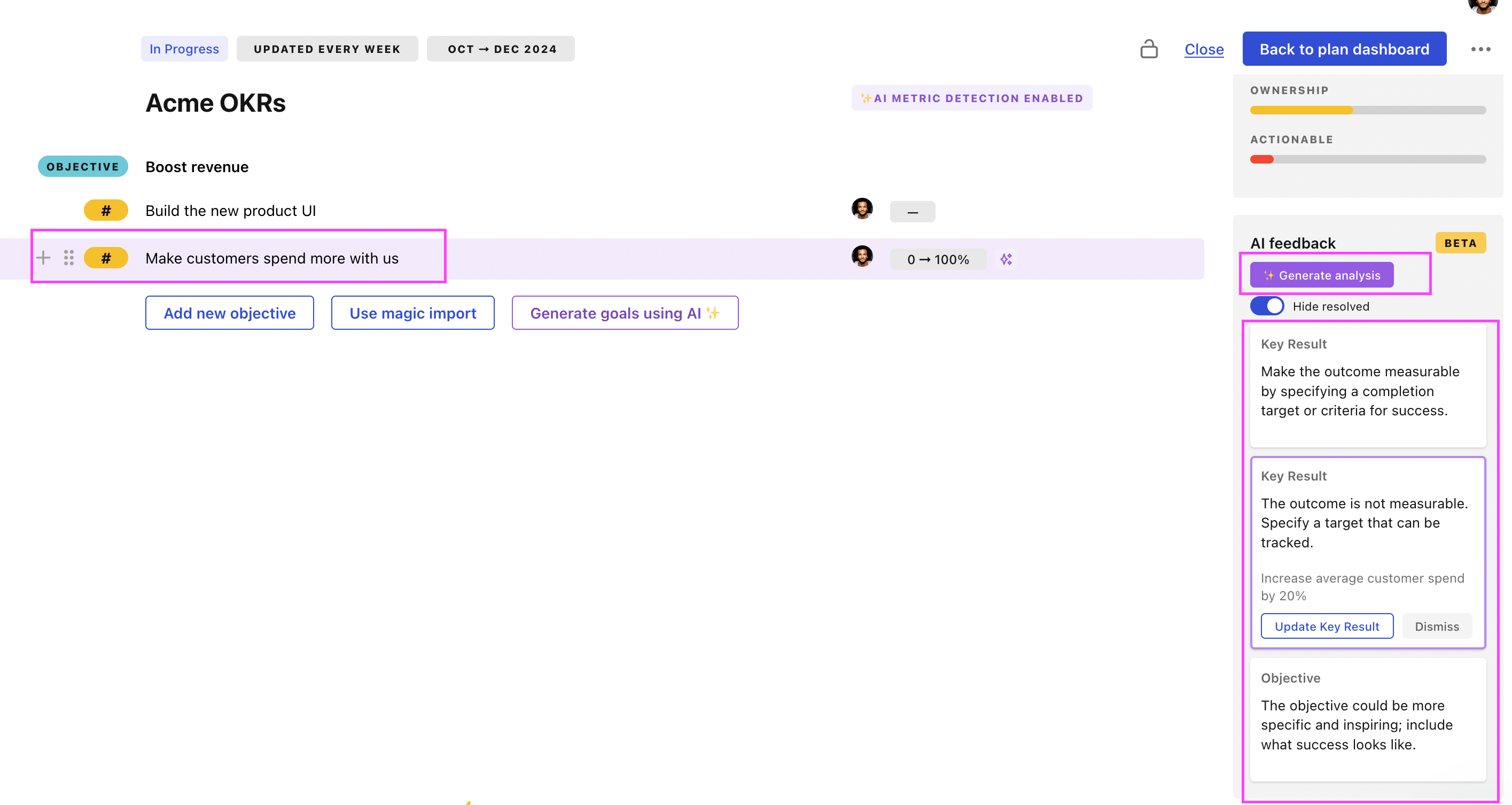
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
Information Security Team OKRs examples
You'll find below a list of Objectives and Key Results templates for Information Security Team. We also included strategic projects for each template to make it easier to understand the difference between key results and projects.
Hope you'll find this helpful!
OKRs to ensure information security solution meets large customer requirements
ObjectiveEnsure information security solution meets large customer requirements
KRAdjust our existing information security solution to match found requirements 100%
Develop and implement changes to fill identified gaps
Identify gaps in the current information security solution
Test and fine-tune the updated security solution
KRIdentify and understand the requirements of 10 major customers by consulting directly
Schedule one-on-one meetings with each of the 10 major customers
Review and analyze all customer feedback to understand requirements
Prepare specific, clear questions for customer consultation
KRSuccessfully pass 10 customer audits confirming solution's compliance with their requirements
Review and understand all customer's requirements for each solution
Conduct internal audits to ensure compliance with requirements
Collect and organize evidence of compliance for audits
OKRs to achieve ISO 27001 certification with an action plan
ObjectiveAchieve ISO 27001 certification with an action plan
KRDevelop and implement necessary policies and procedures to align with ISO 27001 standards
Develop new policies and procedures to meet ISO 27001 standards
Communicate and train employees on the new policies and procedures
Conduct a gap analysis to identify policy and procedure gaps
Regularly review and update policies and procedures to ensure compliance with ISO 27001
KRConduct a comprehensive gap analysis to identify all compliance requirements
KRSuccessfully pass the external ISO 27001 certification audit conducted by a certified auditor
Update and document all necessary processes and procedures in accordance with ISO 27001
Conduct a comprehensive review of the ISO 27001 standard requirements and guidelines
Implement a risk management framework aligned with the ISO 27001 requirements
Train employees on ISO 27001 procedures and their roles in maintaining compliance
KRTrain all employees on information security awareness and best practices
OKRs to attain ISO 27001 certification
ObjectiveAchieve ISO 27001 certification
KRImplement necessary controls and measures to address identified risks and improve information security
Regularly monitor and test the effectiveness of implemented controls and measures
Establish strong access controls and authentication mechanisms to protect sensitive information
Conduct a comprehensive risk assessment to identify vulnerabilities and potential threats
Develop and implement security policies and procedures based on the identified risks
KRTrain all employees on information security policies and procedures to ensure compliance
Develop a comprehensive training program on information security policies and procedures
Conduct mandatory training sessions for all employees on information security policies and procedures
Provide all employees with updated written materials outlining information security policies and procedures
Regularly assess and evaluate employees' understanding of information security policies and procedures
KRConduct a comprehensive risk assessment to identify gaps in information security practices
Develop action plans to address and close the identified gaps in information security practices
Identify potential vulnerabilities and weaknesses in the existing information security infrastructure
Review current information security practices and policies
Assess the potential impact of identified risks on the organization's information and data
KRSuccessfully pass the ISO 27001 certification audit conducted by an accredited external body
Address any identified gaps or weaknesses in the information security controls
Prepare and organize all required documentation and evidence for the audit process
Implement necessary improvements to align with ISO 27001 requirements and best practices
Conduct a thorough internal review of all information security controls and processes
OKRs to full deployment of Ember and Abnormal Security tools in SecOps
ObjectiveFull deployment of Ember and Abnormal Security tools in SecOps
KRAchieve 100% operational status of both tools within the SecOps ecosystem by Week 12
Evaluate current operational status of both tools
Implement changes and verify 100% operational status
Identify necessary upgrades or repairs for both tools
KRTrain IT team on Abnormal Security and Ember tools by the end of Week 6
Prepare materials and resources for the training
Conduct post-training assessment by end of Week 6
Schedule training sessions for IT team on both tools
KRInstall and test Ember and Abnormal Security tools in the SecOps environment by Week 8
Test both tools for effectiveness and efficiency
Install Abnormal Security tool in the SecOps environment
Install Ember tool in the SecOps environment
OKRs to ensure full ISSO compliance through regular audits and security training
ObjectiveEnsure full ISSO compliance through regular audits and security training
KRTrain all new employees about ISSO compliance within their first week of employment
Schedule ISSO compliance training for new hires
Prepare relevant ISSO compliance materials
Conduct compliance training within their first week
KRIncrease the frequency of conducting audits to 100% every week from next quarter
Establish weekly audit schedule for consistent implementation
Monitor and track weekly audit outcomes constantly
Train audit team on the new weekly audit frequency
KRReduce security breaches by 90% through enhanced information security measures this quarter
Implement two-factor authentication for all system logins
Conduct regular cybersecurity training for staff
Update and strengthen all passwords regularly
OKRs to strengthen SOC effectiveness to increase security operations productivity
ObjectiveStrengthen SOC effectiveness to increase security operations productivity
KRReduce false positive alarms from SOC by 30%
Improve analyst training for accurate threat prediction
Regularly update and fine-tune security system settings
Implement advanced anomaly detection algorithms
KRIncrease identification of real threats by 20%
Implement advanced threat detection systems
Conduct regular security awareness training
Strengthen information sharing with allies
KRImprove SOC response time to threats by 15%
Conduct regular response time drills for SOC team
Implement automated threat detection tools for quicker identification
Prioritize high-impact threats for immediate response
OKRs to obtain ISO 27001 certification
ObjectiveAchieve ISO 27001 certification
KRAddress all identified non-conformities and implement corrective actions promptly
Monitor the progress of implemented corrective actions and report any deviations promptly
Develop a corrective action plan outlining steps to resolve each non-conformity
Review and document all identified non-conformities from the assessment
Assign responsible individuals to execute the corrective actions within specified timelines
KRPass the external audit with no major findings and obtain ISO 27001 certification
Conduct regular internal audits to ensure ongoing compliance with ISO 27001 requirements
Work closely with external auditors to address any findings and promptly resolve them
Implement necessary security controls and procedures to address identified gaps
Review existing security controls and identify gaps or areas for improvement
KRConduct a successful internal audit to ensure compliance with ISO 27001 requirements
Develop and implement corrective actions for identified non-compliance issues
Conduct interviews and surveys to gather feedback from employees on compliance practices
Assess and document the effectiveness of existing security controls
Review and update company policies to align with ISO 27001 requirements
KRImplement necessary security controls to comply with ISO 27001 standards
OKRs to implement cutting-edge bot detection technologies for website data
ObjectiveImplement cutting-edge bot detection technologies for website data
KRAchieve 95% accuracy rate in detecting bots using newly implemented technologies
Continuously refine and update the models deployed
Test algorithms with diverse sets of data
Implement new machine learning algorithms for bot detection
KRIntegrate and test 3 selected bot detection technologies on our website
Choose three suitable bot detection technologies for our website
Conduct thorough testing to ensure effectiveness
Implement these technologies into our site's backend
KRIdentify and study 10 new bot detection methods from industry research
Analyze each method's pros, cons, and applicability
Select 10 recent industry research on bot detection methods
Prepare a report summarizing findings
OKRs to implement and maintain SOCII compliance measures
ObjectiveEnsure ongoing SOCII compliance
KRConduct regular testing and auditing to assess SOCII compliance status
KRTrain and educate all relevant teams on SOCII compliance regulations and best practices
KRMonitor and promptly address any SOCII compliance gaps or violations identified
Establish a dedicated team to promptly address and resolve any identified SOCII compliance issues
Implement corrective measures to address identified SOCII compliance gaps promptly
Conduct regular audits to identify any SOCII compliance gaps or violations
Maintain a vigilant monitoring system to detect any new SOCII compliance violations
KRImplement and maintain necessary controls and processes to meet SOCII requirements
Conduct initial assessment of current controls and processes to identify gaps
Develop and document new controls and processes to fulfill SOCII requirements
Regularly monitor and evaluate controls and processes to ensure ongoing compliance
Train and educate employees on the importance and execution of SOCII controls
OKRs to improve the effectiveness and security of Identity Access Management (IAM) initiatives
ObjectiveImprove the effectiveness and security of Identity Access Management (IAM) initiatives
KRReduce IAM-related security incidents by 20%
Implement multi-factor authentication for IAM systems
Update and enforce strict password policies
Conduct regular IAM security training sessions
KRImplement two-factor authentication for all employee IAM accounts
Purchase and install selected two-factor authentication software
Train employees on how to use the new authentication process
Research suitable two-factor authentication software for IAM accounts
KRIncrease IAM user compliance rate by 30%
Implement stricter IAM user permission policies
Provide regular IAM user compliance training
Regularly audit and correct non-compliant IAM users
Information Security Team OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
Focus can only be achieve by limiting the number of competing priorities. It is crucial that you take the time to identify where you need to move the needle, and avoid adding business-as-usual activities to your OKRs.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Having good goals is only half the effort. You'll get significant more value from your OKRs if you commit to a weekly check-in process.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated Information Security Team OKR dashboards
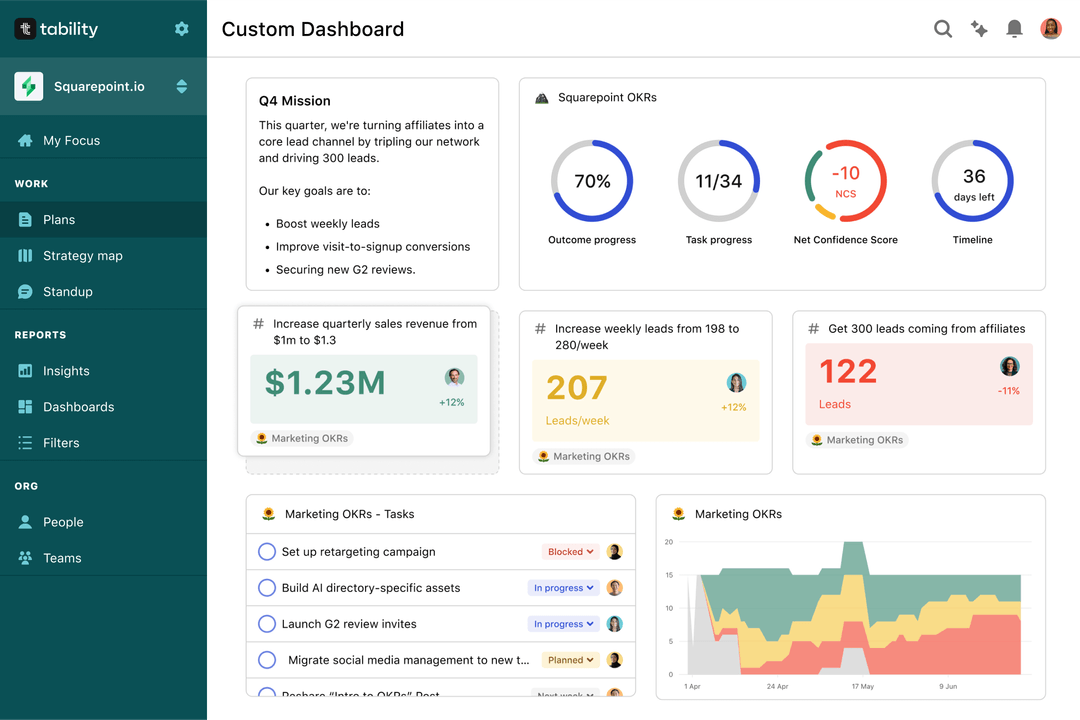
OKRs without regular progress updates are just KPIs. You'll need to update progress on your OKRs every week to get the full benefits from the framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Spreadsheets are enough to get started. Then, once you need to scale you can use Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More Information Security Team OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to enhance user engagement on app and website
OKRs to transform Socotra into a renowned hub for handcraft artisanry
OKRs to secure a substantial promotion at work
OKRs to to maximize clarity and reach in resident communication
OKRs to achieve an 80+ score in work output
OKRs to improve efficiency in resolving health claims denial issues