Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are Data Protection Team OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
Formulating strong OKRs can be a complex endeavor, particularly for first-timers. Prioritizing outcomes over projects is crucial when developing your plans.
To aid you in setting your goals, we have compiled a collection of OKR examples customized for Data Protection Team. Take a look at the templates below for inspiration and guidance.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect Data Protection Team OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
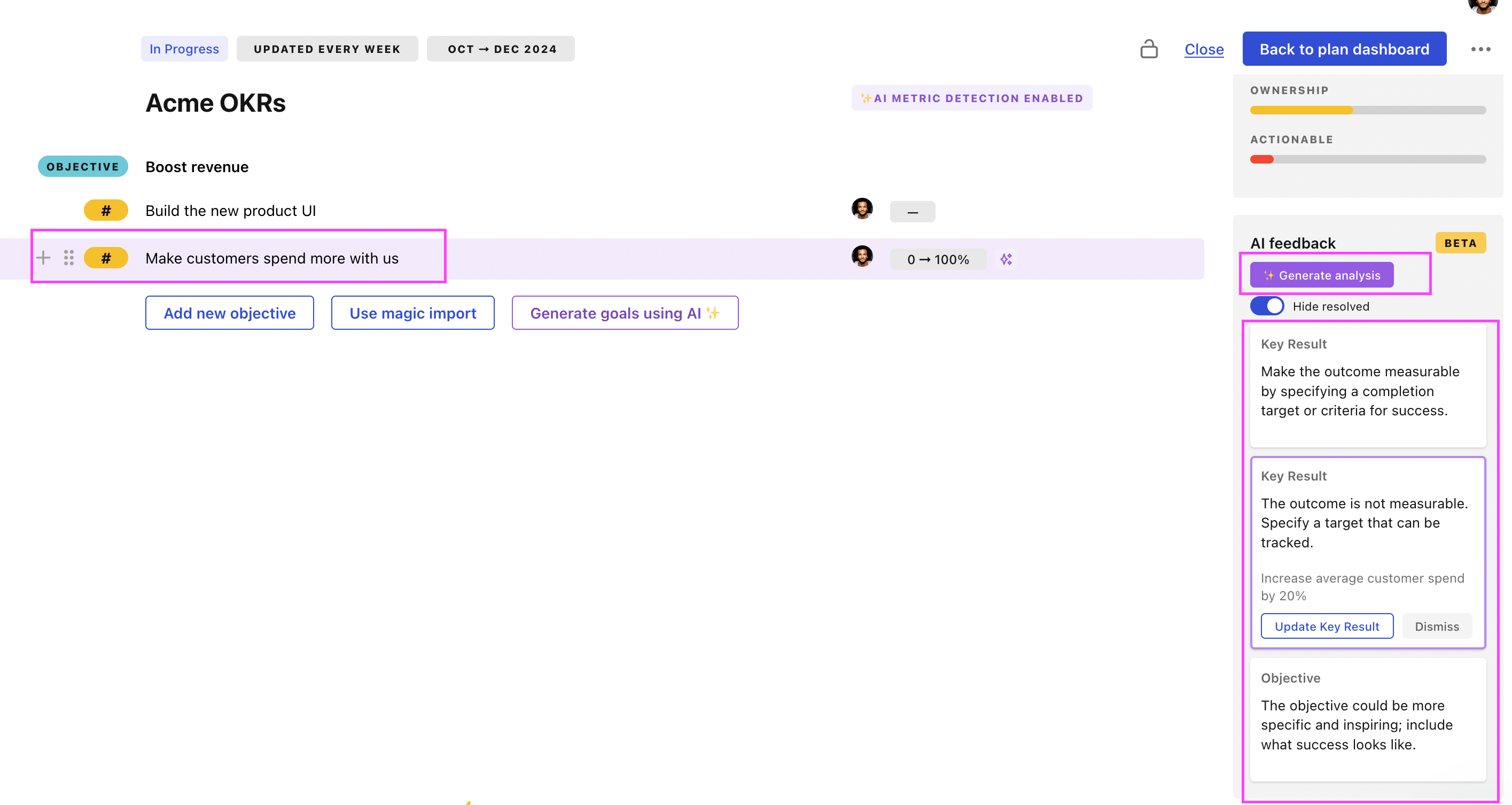
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
Data Protection Team OKRs examples
You will find in the next section many different Data Protection Team Objectives and Key Results. We've included strategic initiatives in our templates to give you a better idea of the different between the key results (how we measure progress), and the initiatives (what we do to achieve the results).
Hope you'll find this helpful!
OKRs to implement and maintain a comprehensive data protection program
ObjectiveStrengthen data protection program
KREnsure compliance with relevant data protection laws and regulations
Regularly review and update data protection practices
Develop and implement policies and procedures for compliance
Identify all applicable data protection regulations
Train employees on data protection laws and regulations
KRConduct a thorough risk assessment and mitigation plan
create contingency plan
develop mitigation strategies
assess likelihood and impact
identify potential risks
KRImplement regular employee training and awareness programs
Schedule regular training sessions
Identify training needs and design a program
Evaluate program effectiveness and make necessary improvements
Encourage employee participation and reward progress
KRRegularly review and update data protection policies and procedures
Train employees on updated policies and procedures
Document all data protection policies and procedures
Regularly audit adherence to policies and procedures
Assign responsibility for policy and procedure review and updates
OKRs to implement SecOps playbooks for Abnormal security and Code42
ObjectiveImplement SecOps playbooks for Abnormal security and Code42
KRDesign, test, and implement the Abnormal Security playbook improving threat response time by 25%
Analyze current Abnormal Security playbook for improvements
Implement and monitor updated playbook in real-time
Design and test modifications for efficiency
KRIdentify and map 10 vital security processes for playbook integration by week 4
Map each process and its components
Identify 10 vital security processes for integration
Ensure integration within playbook by week 4
KRDevelop and enact the Code42 playbook, resulting in a 30% reduction in data loss incidents
Create and refine the comprehensive Code42 playbook
Implement and train staff on the Code42 playbook
Analyze existing data loss scenarios and identify potential vulnerabilities
OKRs to enhance our data leak protection solution's market competitiveness
ObjectiveEnhance our data leak protection solution's market competitiveness
KRDecrease system response time by 25% for improved user experience
Optimize the backend code for better efficiency
Upgrade to faster servers or databases
Implement effective caching strategies for data retrieval
KRIncrease software detection accuracy rate by 20% through advanced algorithms
Implement and test chosen algorithm in software
Research and study advanced algorithm patterns
Analyze data for improvements, refine as necessary
KRTrain customer service team to improve client satisfaction scores by 15%
Incorporate feedback skills improvement in team meetings
Implement comprehensive customer service training program
Establish regular client satisfaction assessments
OKRs to enhance data privacy and cybersecurity measures to safeguard sensitive information
ObjectiveEnhance data privacy and cybersecurity measures to safeguard sensitive information
KRImplement a comprehensive data encryption system across all relevant platforms
Assess current data encryption measures and identify gaps for improvement
Develop and implement a standardized data encryption protocol for all platforms
Conduct regular audits to ensure consistent adherence to the data encryption system
Train employees on proper data encryption practices and its importance in data security
KRConduct regular vulnerability assessments and address identified risks within set timeframes
Quickly prioritize and address identified risks based on severity levels
Schedule regular vulnerability assessments according to established timelines
Establish set timeframes for risk mitigation and ensure timely execution
Develop a clear process for tracking and documenting vulnerability assessment findings
KRIncrease employee awareness and participation in cybersecurity training programs by 25%
Recognize and reward employees who actively participate in cybersecurity training
Create engaging and interactive modules for cybersecurity training programs
Organize lunch and learn sessions to promote employee awareness about cybersecurity threats
Send regular email reminders about upcoming cybersecurity training sessions
KRAchieve a 10% improvement in overall incident response time, ensuring timely mitigation of potential breaches
Streamline incident response processes and eliminate any unnecessary steps for faster response times
Regularly evaluate and improve incident response plans to enhance efficiency and effectiveness
Provide comprehensive training to all personnel involved in incident response procedures
Implement automation tools to expedite the identification and containment of potential breaches
OKRs to establish robust security controls for DHS/ATO and NATO contracts
ObjectiveEstablish robust security controls for DHS/ATO and NATO contracts
KRConduct quarterly maintenance on all the security controls and document findings
Document observations and any maintenance executed
Review all security control systems thoroughly
Perform necessary maintenance on security controls
KRImplement 5 new security measures aligned with DHS/ATO requirements by a 100%
Identify potential security measures that align with DHS/ATO requirements
Implement and test the newly identified security measures
Review existing security measures for any DHS/ATO non-compliance
KRAchieve zero security breaches related to the NATO contracts information
Implement strong encryption on all NATO-related digital communication
Train staff in counter-intelligence and data protection practices
Regularly perform rigorous security audits and fix vulnerabilities
OKRs to establish unparalleled data leak protection solution
ObjectiveEstablish unparalleled data leak protection solution
KRIncrease client satisfaction regarding data security by 25% through feedback surveys
Analyze survey responses for areas of improvement
Develop and execute strategies to address identified issues
Implement consistent client feedback surveys on data security
KRDevelop and implement a cutting-edge encryption system by increasing R&D team by 15%
Execute full implementation of new encryption system
Identify talent to expand R&D team by an additional 15%
Develop advanced encryption system prototype
KRReduce successful cyber attacks on our system by 80%
Implement multi-factor authentication for all system users
Regularly update and patch system software
Conduct frequent cybersecurity training for employees
Data Protection Team OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
Having too many OKRs is the #1 mistake that teams make when adopting the framework. The problem with tracking too many competing goals is that it will be hard for your team to know what really matters.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Setting good goals can be challenging, but without regular check-ins, your team will struggle to make progress. We recommend that you track your OKRs weekly to get the full benefits from the framework.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated Data Protection Team OKR dashboards
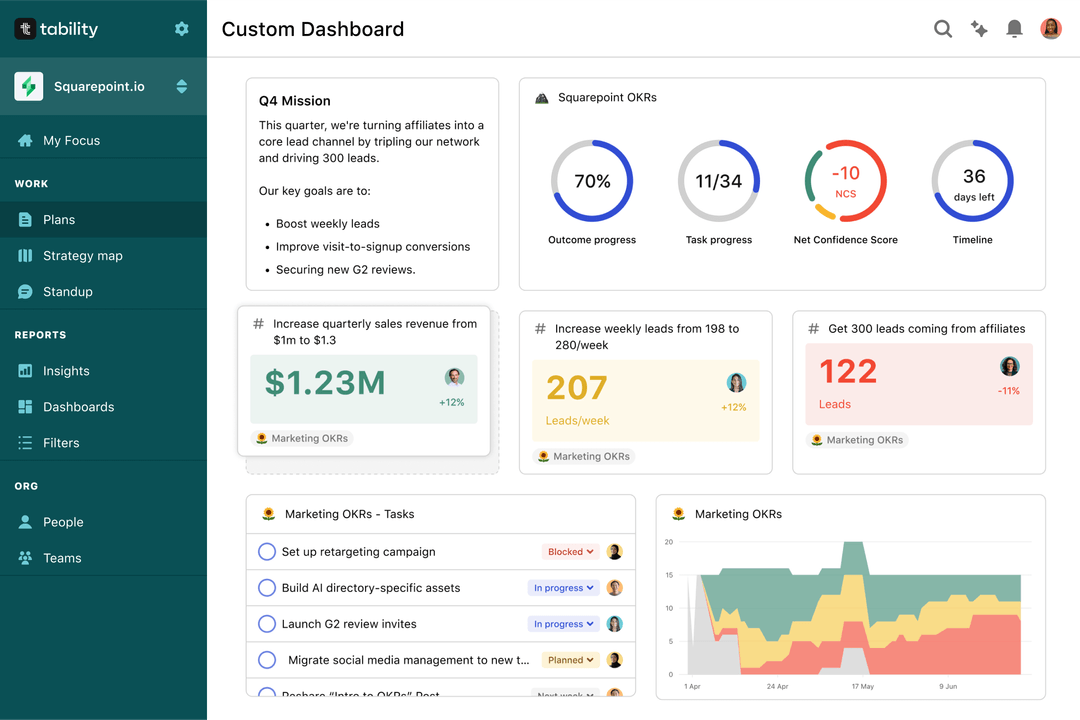
The rules of OKRs are simple. Quarterly OKRs should be tracked weekly, and yearly OKRs should be tracked monthly. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Spreadsheets are enough to get started. Then, once you need to scale you can use Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More Data Protection Team OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to promote cultural humility for diverse, healthy team building
OKRs to enhance Product Service Management Efficiency
OKRs to author comprehensive ADRs for Google Cloud Platform at FinTech company
OKRs to implement routine financial stress-testing scenarios
OKRs to boost customer loyalty and revenue through increased site traffic
OKRs to streamline all business processes through automation