OKR template to enhance Identity Access Management for large scale clients
This leadership OKR template is a strong starting point for teams that need better alignment, clearer priorities, and more disciplined goal tracking.
Use it to turn a business priority into a measurable objective, then review progress weekly so your team can adjust execution before the quarter gets away from you.
Your OKR template
The second aspect of the OKR focuses on incorporating new features as per client input into a majority of the accounts. The approach includes designing those features, integrating them into the system, and collecting and categorizing client feedback to determine desired functionalities.
The third component of the OKR is to significantly reduce access-related security incidents. The initiatives put in place include a dual-factor authentication process for users, regular audits of access controls and permissions, and an updated, robust password policy.
This OKR overall focuses on delivering a superior user experience by boosting system performance, personalizing client features, and substantially strengthening security protocols.
ObjectiveEnhance Identity Access Management for large scale clients
KRIncrease system response time by 20% for enhanced user experience
Identify and eliminate any unnecessary background processes
Upgrade system hardware to improve performance
Optimize code for increased efficiency
KRImplement new features from client input in 60% of all accounts
Design and develop the requested features
Implement the new features in the chosen accounts
Collect and categorize client input about desired features
KRReduce access-related security incidents by 30% through stronger protocols
Implement two-factor authentication for all system users
Conduct frequent audits of access controls and permissions
Regularly update passwords and maintain a strong password policy
Tability: the best OKR software for results-driven teams
OKRs should be tracked weekly to be effective, and Tability is the perfect tool for that.
Tability is the best OKR software that embraces modern principles to help teams set better goals, monitor execution, and get help to achieve their objectives faster.
With Tability you can:
- Get an OKR agent that can review existing OKRs, suggest improvements, and monitor execution
- Connect your OKRs and team goals to Jira, ClickUp, Linear, Asana, and more
- Automate reporting with integrations and built-in dashboard
You can import OKRs in seconds with the magic importer, and start executing your goals in no time.
Step 1. Sign up for a free Tability account
Go tohttps://tability.app/signup and create your account (it's free!)
Step 2. Create a plan
Follow the steps after your onboarding to create your first plan, you should get to a page that looks like the picture below.
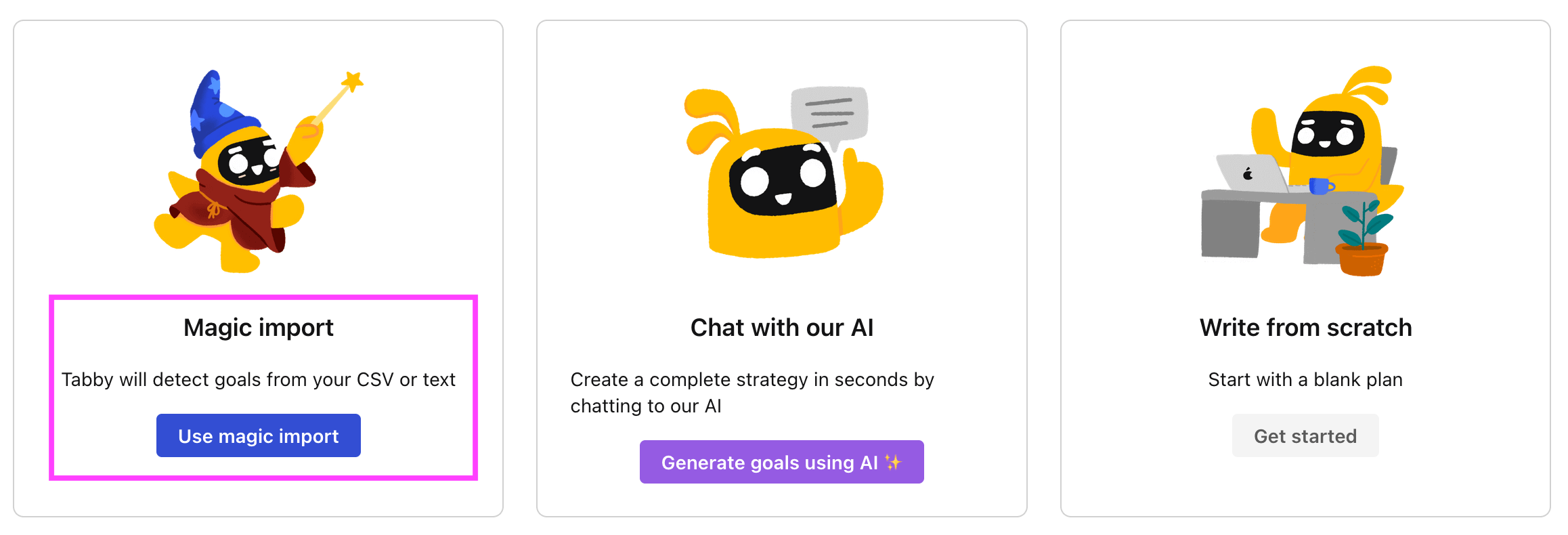
Step 3. Use the magic importer
Click on Use magic import to open up the Magic Import modal.
Now, go back to the OKR examples, and click on Copy on the example that you’d like to use.
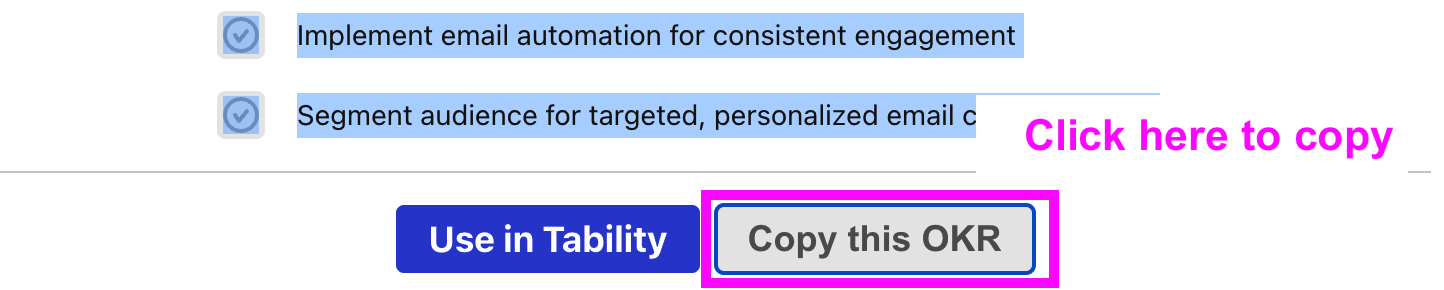
Paste the content in the text import section. Don’t worry about the formatting, Tability’s AI will be able to parse it!
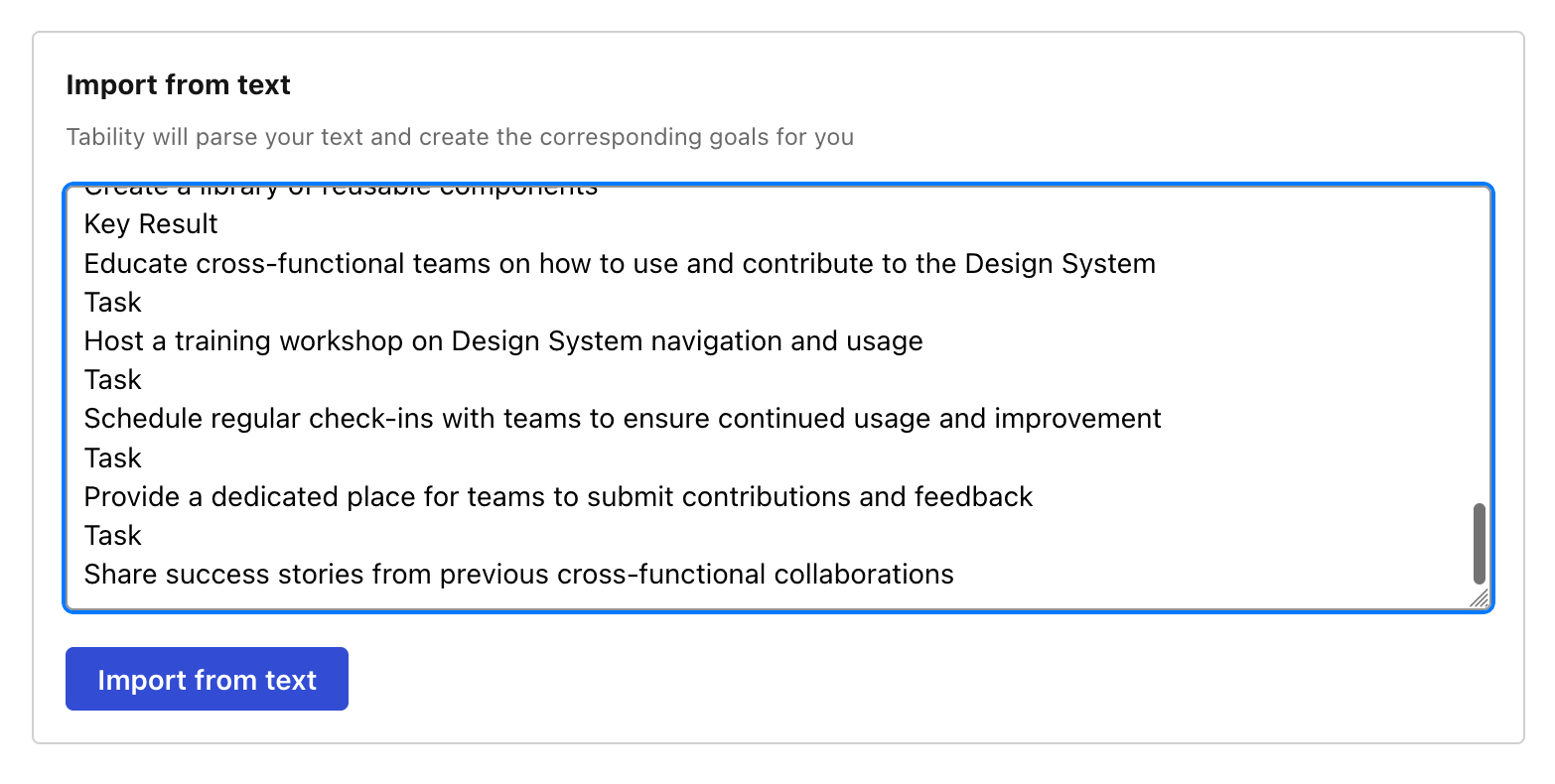
Now, just click on Import from text and let the magic happen.
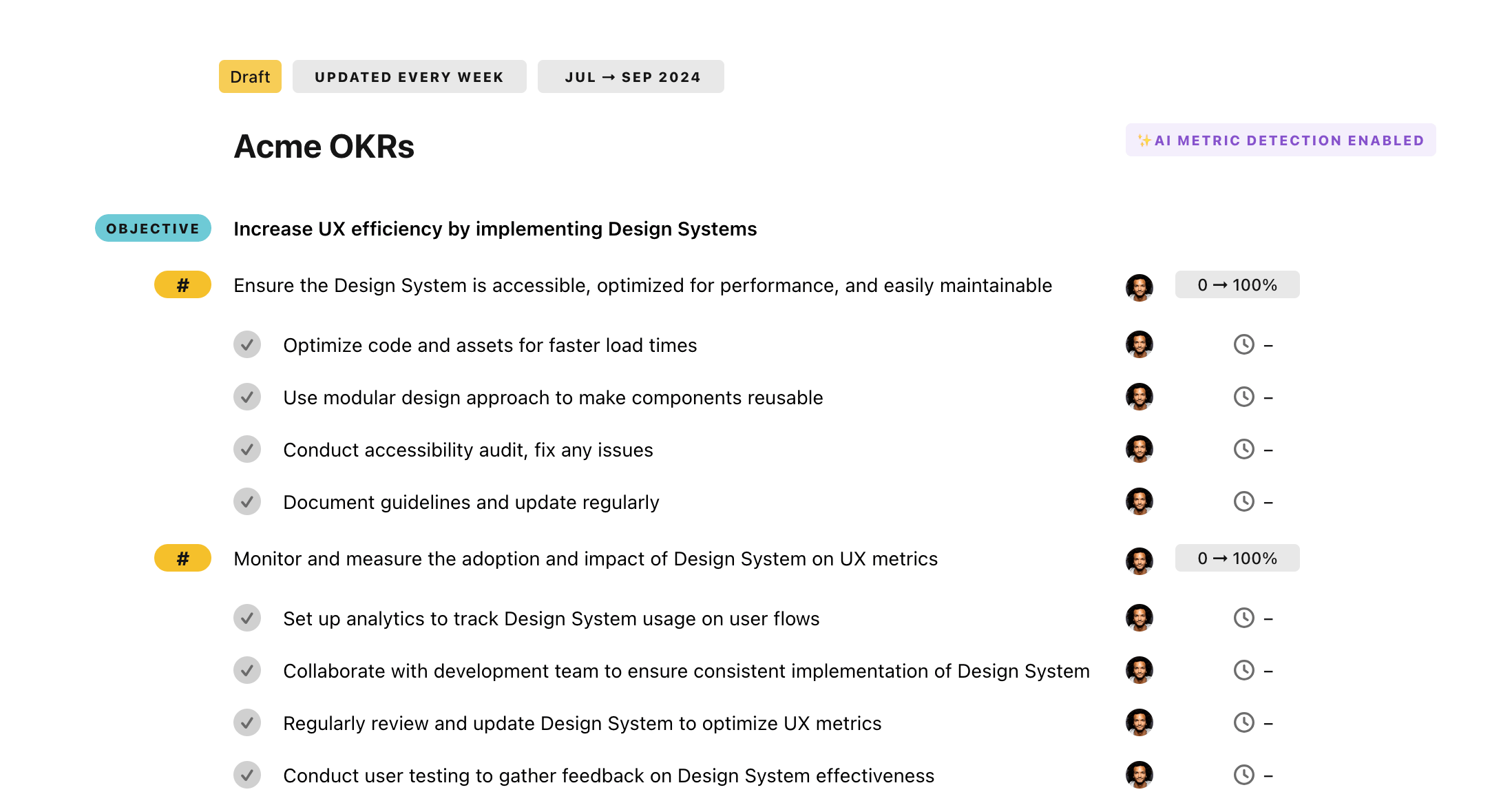
Once your example is in the plan editor, you will be able to:
- Edit the objectives, key results, and tasks
- Click on the target 0 → 100% to set better target
- Use the tips and the AI to refine your goals
Step 4. Publish your plan
Once you’re done editing, you can publish your plan to switch to the goal-tracking mode.
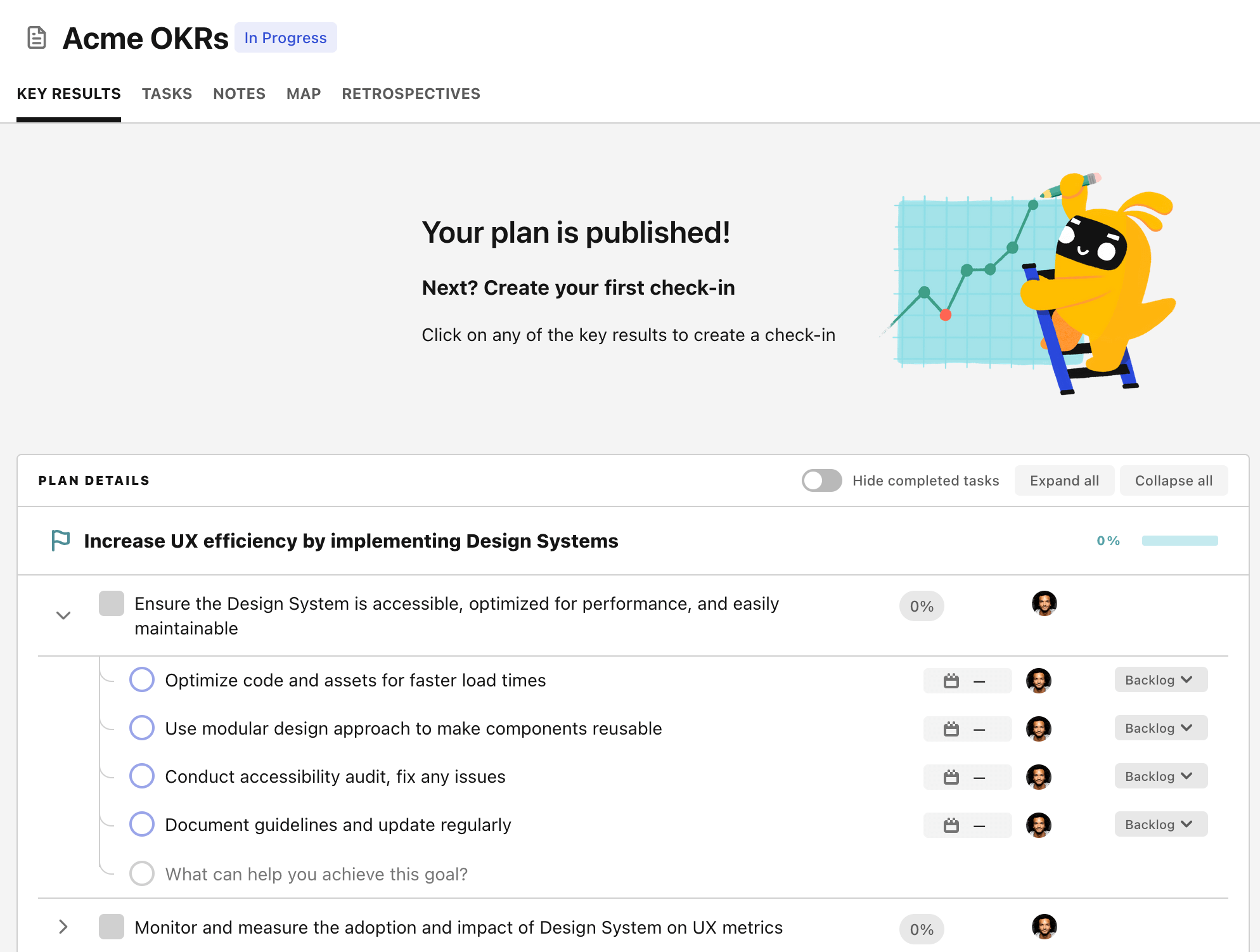
From there you will have access to all the features that will help you and your team save hours with OKR reporting.
- 10+ built-in dashboards to visualise progress on your goals
- Weekly reminders, data connectors, and smart notifications
- 9 views to map OKRs to strategic projects
- Strategy map to align teams at scale