OKR template to strengthen network security through enhanced logging capabilities
Your OKR template
The second aspect focuses on elevating network security by establishing an intrusion detection system (IDS) equipped with real-time monitoring capabilities. This stage doesn't outline specific initiatives, suggesting adaptability and allowing for a customized approach based on the organization's specific network structure and vulnerabilities.
Thirdly, this OKR aims to enhance incident response effectiveness by integrating logging data with a Security Information and Event Management (SIEM) system. Ongoing optimization of the integrated system, standardized alerting rules based on the data, and ensuring all relevant data sources are included in the system are all key areas of focus.
Finally, regular review and analysis of network log data to identify and swiftly address security vulnerabilities forms a critical part of this OKR. This includes scheduling frequent reviews, generating informative reports, implementing measures to tackle identified vulnerabilities, and using appropriate security software to monitor potential threats.
ObjectiveStrengthen network security through enhanced logging capabilities
KRImplement centralized logging infrastructure to capture and store network activity data
Regularly monitor and maintain the centralized logging infrastructure to ensure uninterrupted data capture
Assess existing network infrastructure to identify suitable centralized logging solutions
Configure the centralized logging infrastructure to collect and store the network activity data
Determine the appropriate tools and technologies required for capturing network activity data
KRIncrease network security by configuring an intrusion detection system (IDS) with real-time monitoring capabilities
KRImprove incident response effectiveness by integrating logging data with a security information and event management (SIEM) system
Regularly review and fine-tune the integration and alerting processes to optimize incident response
Analyze current logging data sources and identify gaps for integration with the SIEM system
Develop standardized alerting rules within the SIEM system based on integrated logging data
Configure the SIEM system to ingest and aggregate logging data from all relevant sources
KRIdentify and resolve security vulnerabilities by regularly reviewing and analyzing network log data
Set up a regular schedule for reviewing and analyzing network log data
Generate reports based on network log data analysis to prioritize and address vulnerabilities
Implement necessary measures to resolve identified security vulnerabilities promptly and effectively
Use security software to identify and monitor potential security vulnerabilities
How to edit and track OKRs with Tability
You'll probably want to edit the examples in this post, and Tability is the perfect tool for it.
Tability is an AI-powered platform that helps teams set better goals, monitor execution, and get help to achieve their objectives faster.
With Tability you can:
- Use AI to draft a complete set of OKRs in seconds
- Connect your OKRs and team goals to your project
- Automate reporting with integrations and built-in dashboard
Instead of having to copy the content of the OKR examples in a doc or spreadsheet, you can use Tability’s magic importer to start using any of the examples in this page.
The import process can be done in seconds, allowing you to edit OKRs directly in a platform that knows how to manage and track goals.
Step 1. Sign up for a free Tability account
Go tohttps://tability.app/signup and create your account (it's free!)
Step 2. Create a plan
Follow the steps after your onboarding to create your first plan, you should get to a page that looks like the picture below.
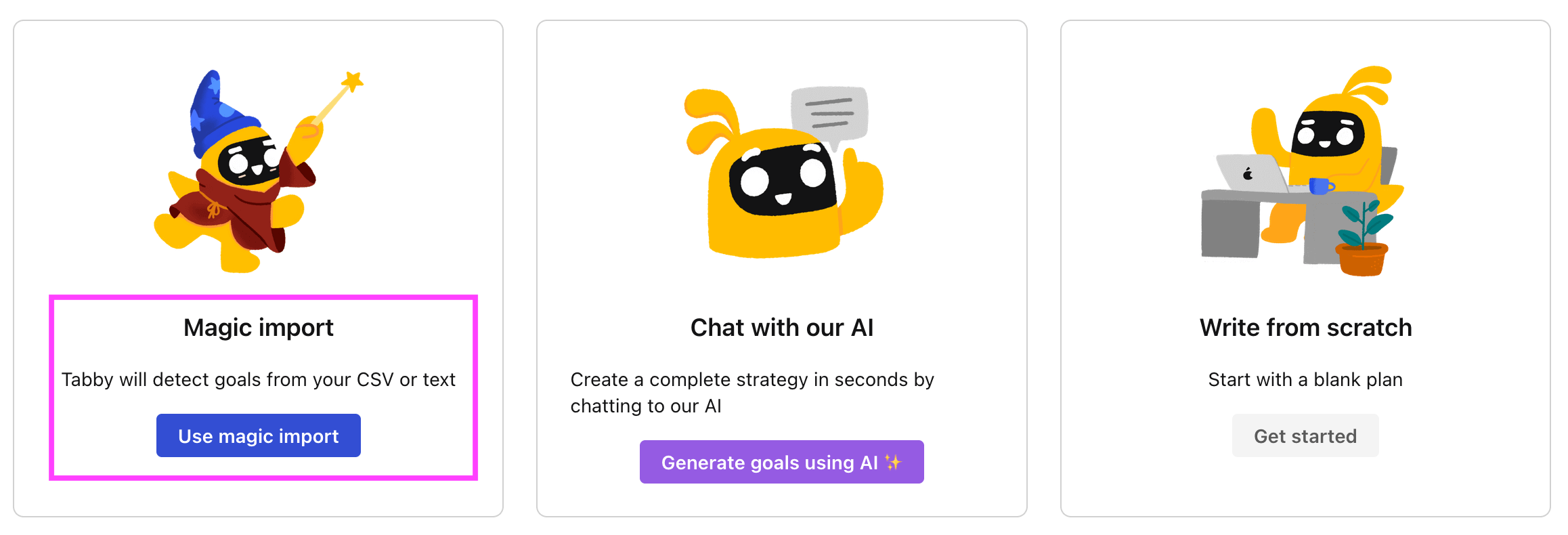
Step 3. Use the magic importer
Click on Use magic import to open up the Magic Import modal.
Now, go back to the OKR examples, and click on Copy on the example that you’d like to use.
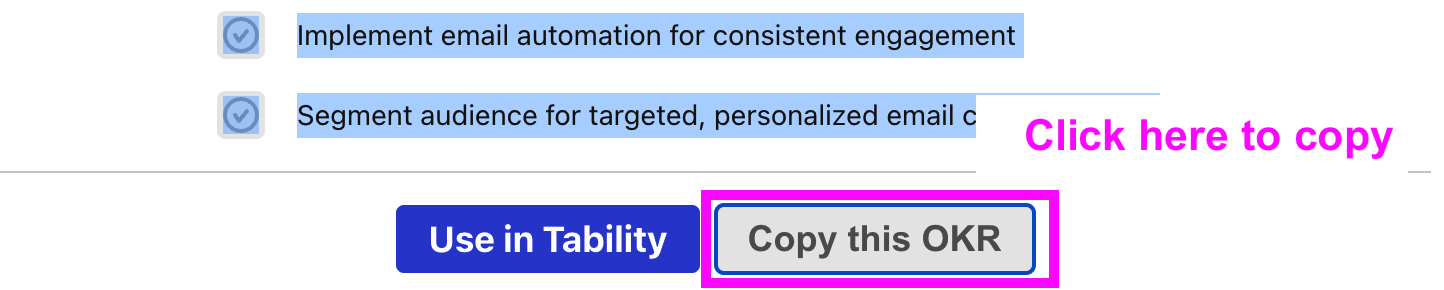
Paste the content in the text import section. Don’t worry about the formatting, Tability’s AI will be able to parse it!
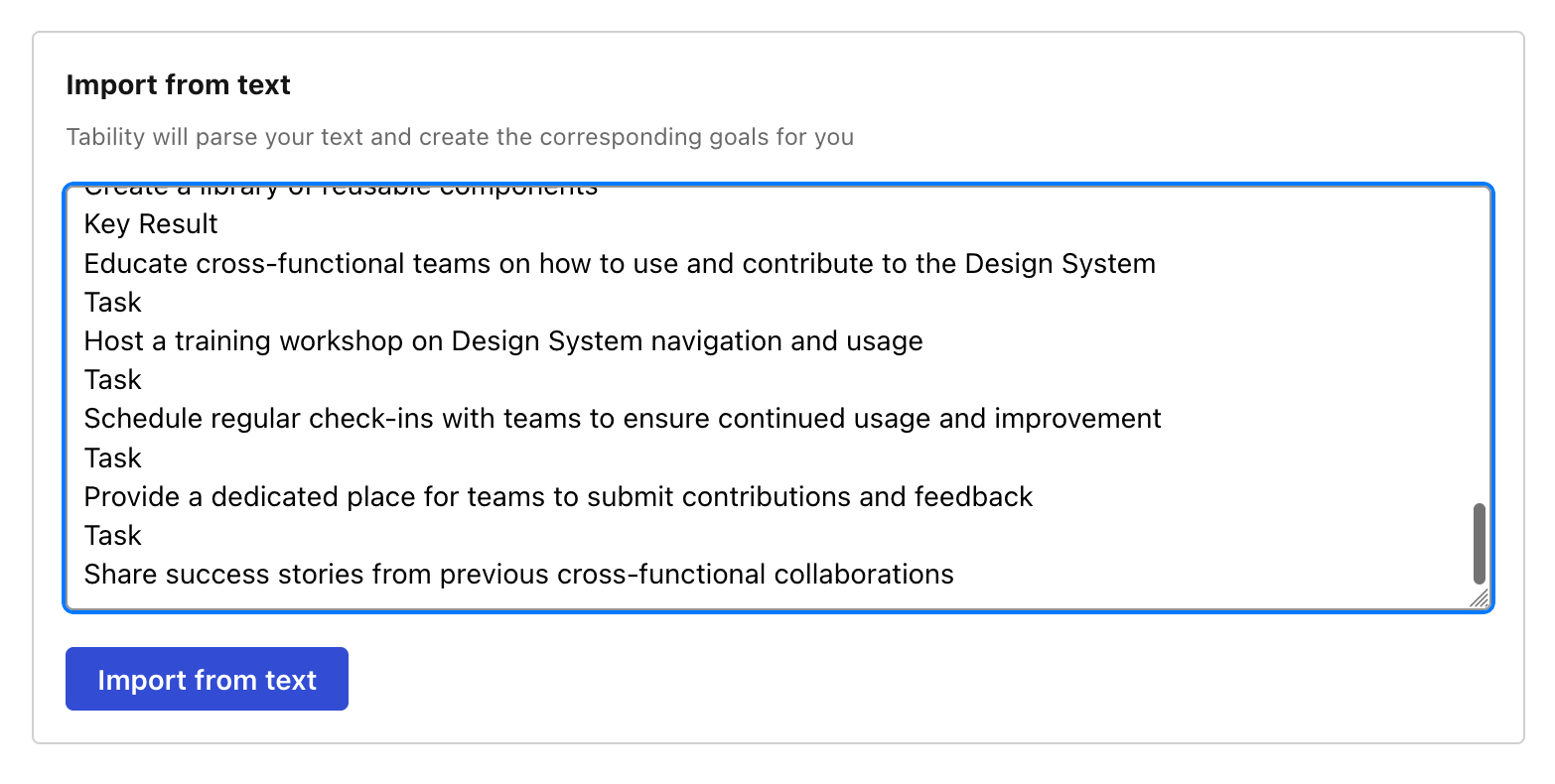
Now, just click on Import from text and let the magic happen.
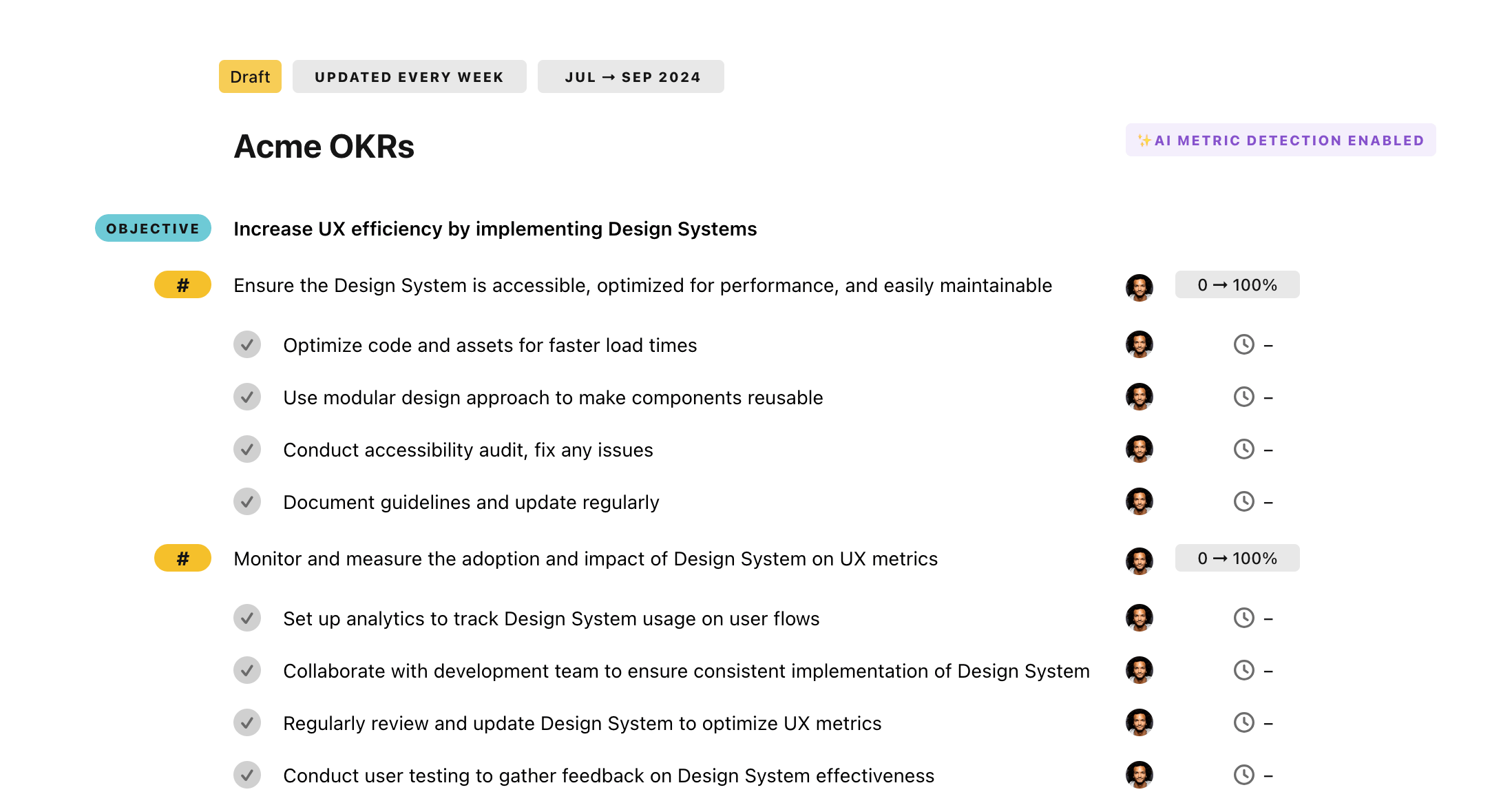
Once your example is in the plan editor, you will be able to:
- Edit the objectives, key results, and tasks
- Click on the target 0 → 100% to set better target
- Use the tips and the AI to refine your goals
Step 4. Publish your plan
Once you’re done editing, you can publish your plan to switch to the goal-tracking mode.
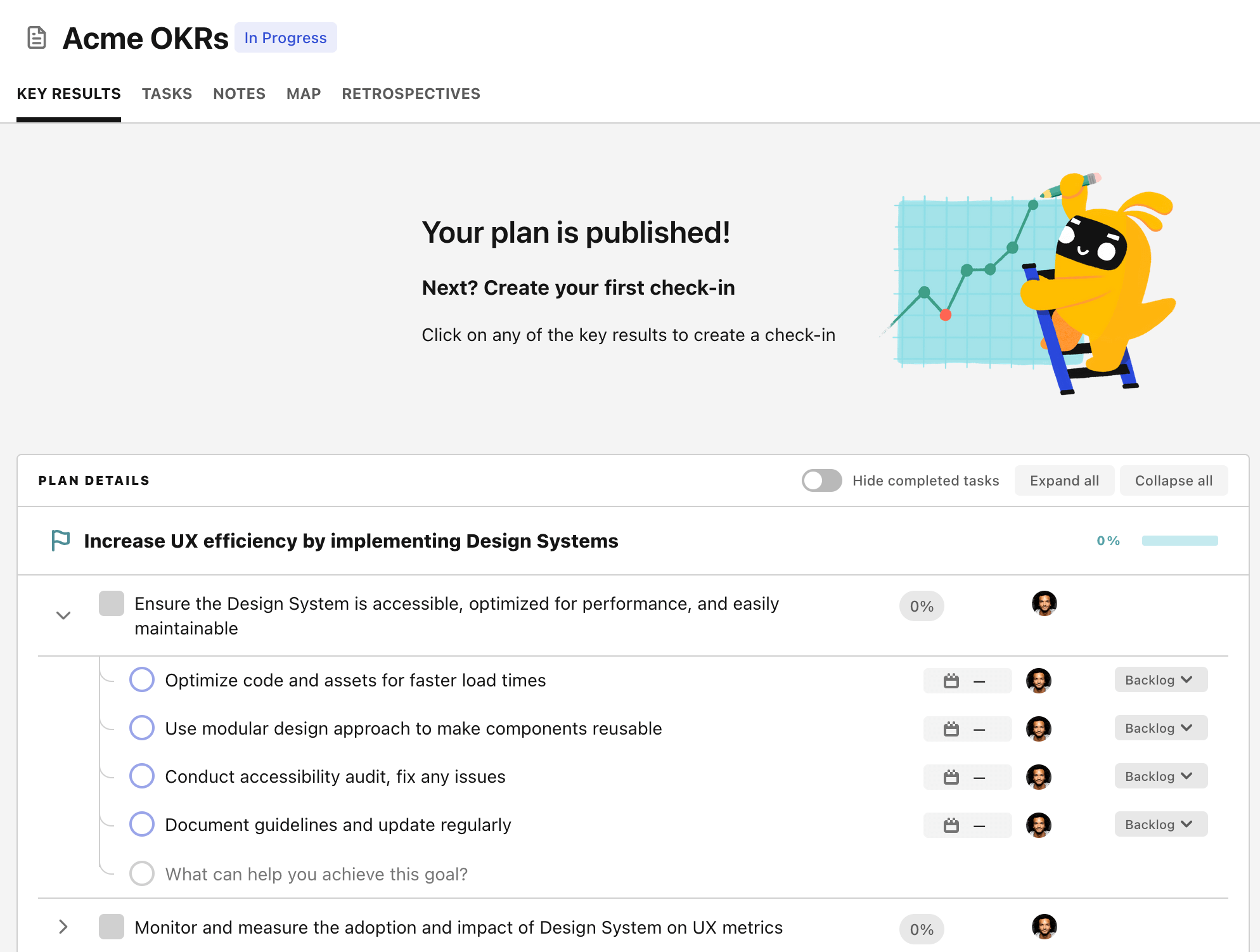
From there you will have access to all the features that will help you and your team save hours with OKR reporting.
- 10+ built-in dashboards to visualise progress on your goals
- Weekly reminders, data connectors, and smart notifications
- 9 views to map OKRs to strategic projects
- Strategy map to align teams at scale